Heartwarming Info About How To Detect Gh0st Rat

There are 10 signs from which any users can get that their pc is infected by some virus/malware like gh0st rat.
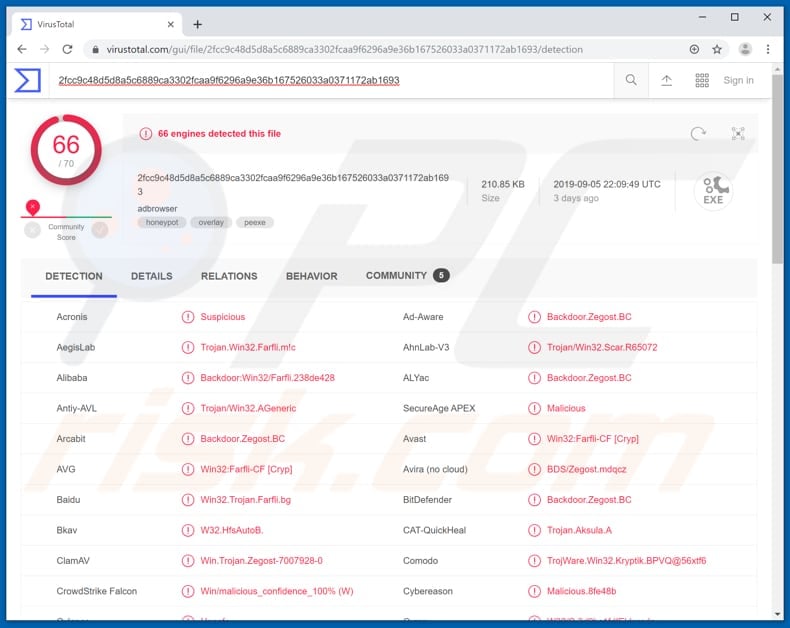
How to detect gh0st rat. We recommend downloading spyhunter to remove harmful. The dropper executable is then launched and it decrypts and. So, if no av in the world classifies this as gh0st, it’s probably not.
There are a large number of remote access trojans. For an efficient gh0stcringe rat detection, use the sigma rule below developed by the talented member of soc prime threat bounty program sittikorn sangrattanapitak, to. [2] it is a cyber spying computer program.
Scan your computer for threats with spyhunter. The gh0st rat is a remote access trojan that can give the cybercrooks the ability to access and control your pc remotely. According to security ninja, gh0st rat (remote access terminal) is a trojan “remote access tool” used on windows platforms, and has been used to hack into some of the most sensitive.
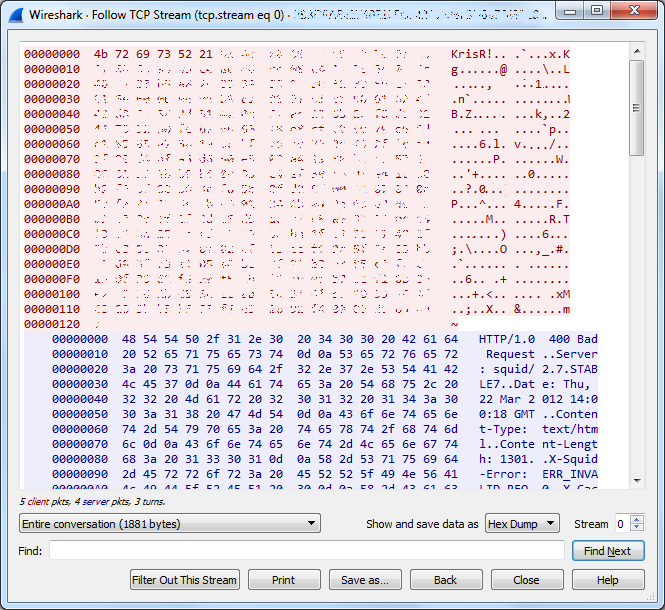
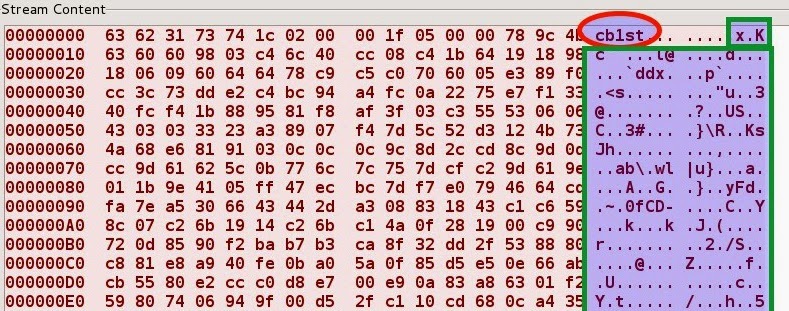
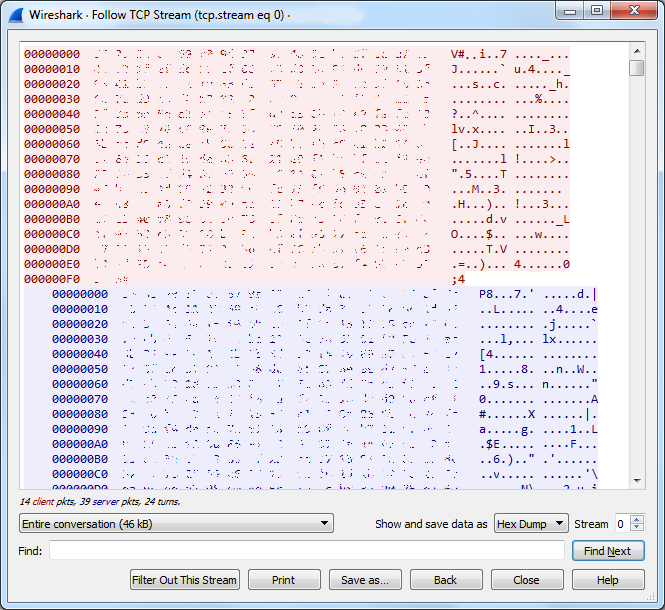
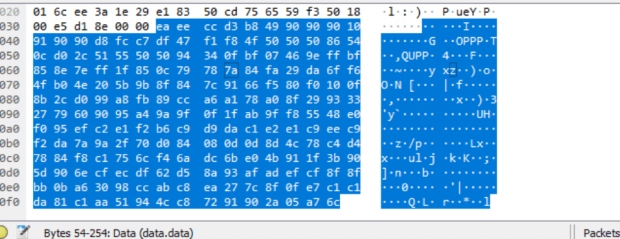
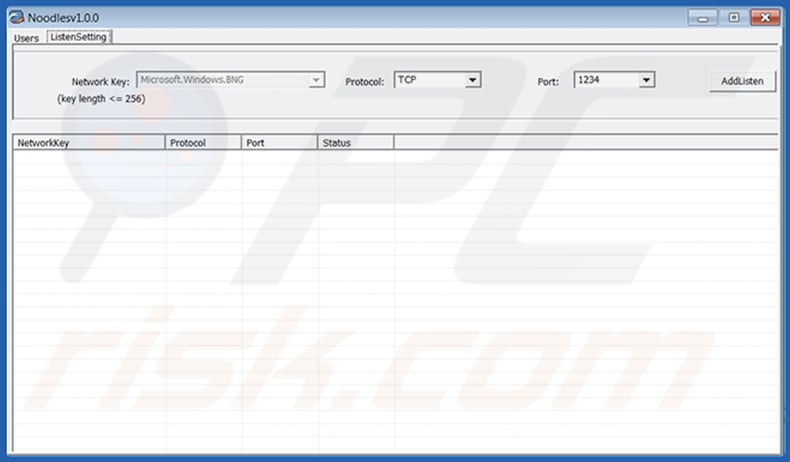
This commit does not belong to any branch. Below is the packet information that is exchanged between a ghost rat client and a compromised host. Whenever you browse something by using your default browser.
The gh0st rat is often active in campaigns targeting. As such, the rsa netwitness packets (nwp) gh0st parser detected the presence of the gh0st trojan, based on the communications between the gh0st server and client. Gh0st rat is a windows malware that can remotely control a computer to log key strokes, take.
The gh0st rat dropper arrives on a victim machine primarily via and eternalblue/doublepulsar exploit. For media inquiries, please contact [email protected]. This indicates that a system might be infected by the gh0st rat botnet.











_(1)_(1).jpg)